
North Korea-linked Lazarus Group Breaches Bitrefill, Exposes 18,500 Purchase Records
Key Takeaways
- Lazarus Group conducted March 1 cyberattack on Bitrefill, draining hot wallets.
- About 18,500 purchase records were exposed.
- Bitrefill will cover losses from its operational capital.
Attack Overview
Cryptocurrency e-commerce platform Bitrefill fell victim to a significant cyberattack on March 1, 2026.
“Bitrefill accuses North Korea-linked Lazarus hacker group for compromising 18,500 purchase records Bitrefill will cover the losses from operational capital”
North Korea-linked Lazarus Group hackers compromised its infrastructure, drained cryptocurrency hot wallets, and exposed approximately 18,500 purchase records containing sensitive customer information.

The breach represents another major incident attributed to the notorious Lazarus Group, which has been linked to some of the largest cryptocurrency thefts in recent history.
This includes a heist exceeding $1 billion from Bybit the previous year.
Bitrefill, a platform designed to enable cryptocurrency users to purchase digital gift cards and pay bills online through partnerships with major retailers like Amazon, Apple, Walmart, and Uber, confirmed the incident.
The company emphasized that customer balances remain safe despite the attack.
Attack Vector
The attack originated from a compromised employee laptop that contained legacy credentials, allowing attackers to access production keys and escalate privileges across Bitrefill's infrastructure.
According to the company's incident report, the breach began when hackers recovered credentials from the laptop that provided access to sensitive production data snapshots.

Once inside, the attackers systematically moved deeper into Bitrefill's systems, targeting both its internal database segments and cryptocurrency hot wallets.
The intruders also exploited the company's gift card inventory systems, making fraudulent purchases with vendors through compromised supply chain channels.
This sophisticated attack pattern suggests a well-planned operation designed to maximize financial gain while minimizing detection.
Data Exposure
The breach exposed sensitive data from approximately 18,500 purchase records, including email addresses, cryptocurrency payment addresses, and metadata such as IP addresses.
“Bitrefill accuses North Korea-linked Lazarus hacker group for compromising 18,500 purchase records Bitrefill will cover the losses from operational capital”
Among these records, around 1,000 contained customer names in encrypted form, which Bitrefill is treating as potentially exposed due to the possibility that attackers may have obtained the corresponding encryption keys.
Despite the significant data exposure, Bitrefill maintains that it stores minimal personal data and does not require mandatory know-your-customer verification for most transactions.
The company clarified that any KYC-related information is handled by external providers and not stored within Bitrefill's systems, reducing the overall risk to customer privacy.
The investigation found no evidence that the attackers accessed Bitrefill's full database or that customer data was their primary objective.
Response & Impact
In response to the security breach, Bitrefill immediately took its systems offline to contain the breach across its global operations, with services remaining unavailable for approximately four days while the company worked to address the incident.
The company collaborated extensively with external security researchers, including specialized incident response firms like zeroShadow, SEAL911, and RecoverisTeam, as well as blockchain analysts and law enforcement to investigate the breach.

Despite the significant disruption, Bitrefill has since restored most services to normal levels, including payment processing and account access.
The company has committed to covering all financial losses from the attack using its operational capital, though it did not disclose the exact amount stolen from the hot wallets.
This incident highlights the ongoing challenges in cryptocurrency security and the need for stronger supply-chain and penetration testing defenses across the ecosystem.
Attribution
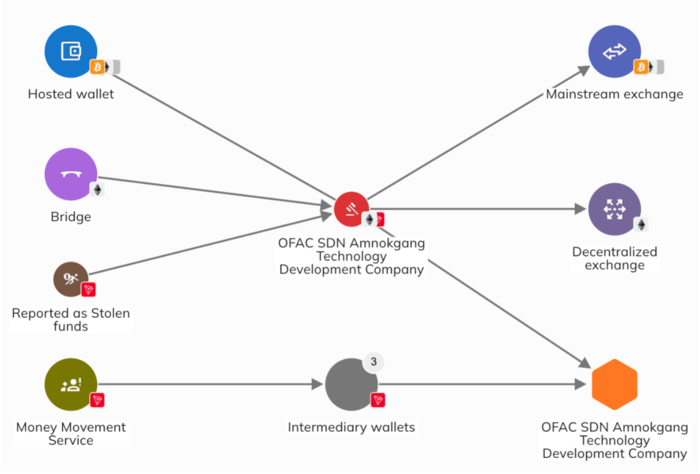
Bitrefill attributed the attack to North Korea's Lazarus Group based on multiple indicators including similarities in malware patterns, reused infrastructure such as IP addresses and email accounts, and on-chain transaction analysis.
“Bitrefill Hack Exposes Wallets and Gift Card Systems as North Korean Links Emerge Bitrefill said on March 17 that a cyberattack earlier this month compromised its hot wallets, parts of its database, and gift card purchasing systems after attackers gained access through a single employee laptop and used legacy credentials containing production secrets”
While the company did not present this attribution as definitively confirmed, citing the sophisticated nature of the attack, multiple cybersecurity firms including zeroShadow, SEAL911, and RecoverisTeam supported the investigation.

The Lazarus Group, often associated with North Korea, has been responsible for numerous high-profile cryptocurrency heists through its specialized subgroup Bluenoroff.
This latest attack continues the group's pattern of targeting cryptocurrency platforms and exchanges, demonstrating their continued capability and focus on financial cyber operations.
The incident serves as a stark reminder of the persistent threat posed by state-sponsored hacking groups in the cryptocurrency ecosystem.
More on Crypto

Mastercard to acquire BVNK for up to $1.8B to accelerate stablecoin strategy.
24 sources compared

Boris Johnson Calls Bitcoin a Ponzi Scheme; Saylor, Eric Trump Defend Crypto
12 sources compared

Bybit Pay Joins Mastercard Crypto Credential Network, Lets Users Send Digital Assets Using Verified Aliases
10 sources compared
U.S. Treasury Freezes Crypto Network Feeding Nearly $800 Million To North Korea's Weapons Programs
10 sources compared