
North Korean Intel Runs Six-Month Con to Hack $270 Million from Drift
Key Takeaways
- North Korea-linked actors conducted a six-month intelligence operation against Drift.
- Attackers posed as a trading firm, met Drift contributors abroad, deposited $1M, waited six months.
- Loss estimated between $270 and $286 million.
Elaborate Infiltration
Drift Protocol was hacked for $270 million in a six-month North Korean intelligence operation.
“Drift says $270 million exploit was a six-month North Korean intelligence operation Attackers posed as a trading firm, met Drift contributors in person across multiple countries, deposited $1 million of their own capital, and waited half a year before executing the drain CoinDesk detailed earlier this week”
Attackers posed as a quantitative trading firm, meeting contributors in person across multiple countries.

They deposited over $1 million of their own capital and integrated an Ecosystem Vault.
The exploit did not stem from a smart contract bug but from compromised administrative controls.
Complex Attack Vectors
Forensic analysis identified two likely intrusion vectors: a malicious code repository and a TestFlight application.
A known vulnerability in VSCode and Cursor editors may have enabled silent code execution.

Drift immediately suspended all protocol functions.
Mandiant was engaged for investigation.
Aftermath and Recovery
Drift's native token plunged from $0.07 to around $0.03.
“Drift says $270 million exploit was a six-month North Korean intelligence operation Attackers posed as a trading firm, met Drift contributors in person across multiple countries, deposited $1 million of their own capital, and waited half a year before executing the drain CoinDesk detailed earlier this week”
The team began sending on-chain messages to wallets holding stolen crypto.
The attack was attributed with medium-high confidence to UNC4736.
Such long-con, identity-rich operations expose deep weaknesses in multisig-based security.
More on Crypto
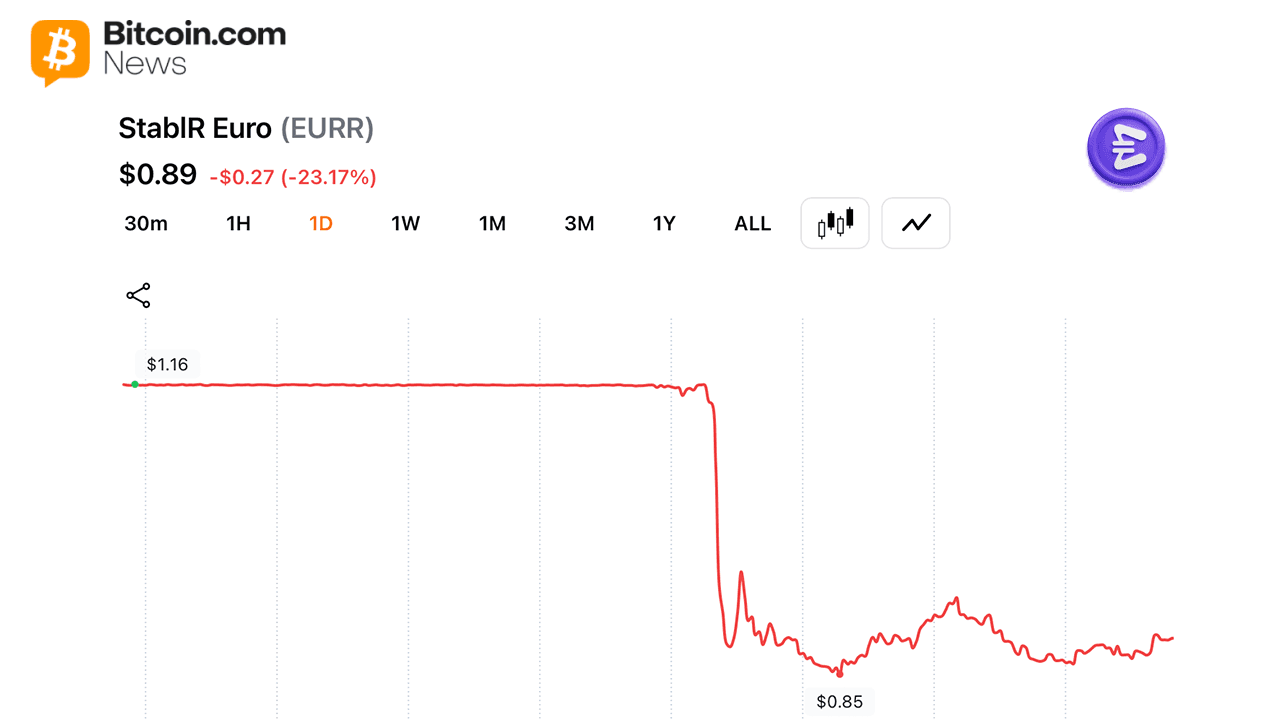
StablR Exploit Drains $2.8M, Malta Issuer Says EURR and USDR Depeg
11 sources compared

Santiment Says $1.26B Bitcoin ETF Outflows Could Signal A Contrarian Buy
11 sources compared

Bitcoin Pizza Day Marks Laszlo Hanyecz’s 10,000-Bitcoin Deal For Two Papa John’s Pizzas
16 sources compared

Iran and Oman Negotiate Strait of Hormuz Ship Payment System Amid U.S. Warnings
16 sources compared