
FBI Seizes Handala Websites After Destructive Stryker Cyberattack
Key Takeaways
- FBI seized two Handala domains following the destructive Stryker cyberattack.
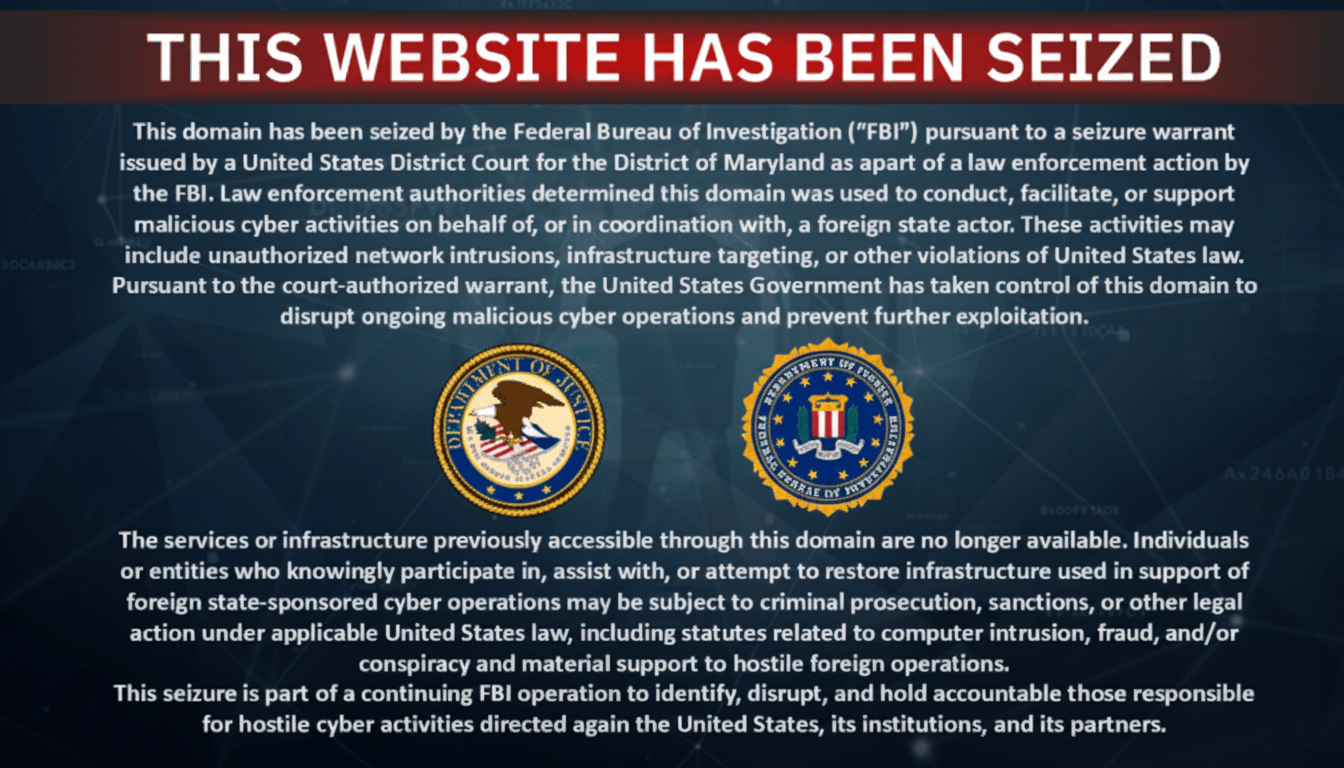
- Domains display seizure notices under a federal seizure warrant.
- U.S. authorities say the domains facilitated malicious activity in coordination with a foreign state actor.
FBI Seizure Action
The Federal Bureau of Investigation (FBI) has seized two websites belonging to the Handala hacktivist group.
“The FBI has seized two websites used by the Handala hacktivist group after the threat actors conducted a destructive cyberattack on medical technology giant Stryker that wiped approximately 80,000 devices”
The seizure follows the group's destructive cyberattack on medical technology giant Stryker that wiped approximately 80,000 devices.

The seized domains, handala-redwanted[.]to and handala-hack[.]to, now display official seizure notices issued by the FBI.
These notices were issued under a warrant from the District Court for the District of Maryland.
The seizure messages state the domains were used for malicious cyber activities on behalf of or in coordination with a foreign state actor.
These activities include unauthorized network intrusions, infrastructure targeting, or violations of U.S. law.
The FBI action represents a significant disruption of the group's online infrastructure and propaganda operations.
Handala Group Profile
Handala, also known as Handala Hack Team, Hatef, or Hamsa, is an Iranian-linked, pro-Palestinian hacktivist collective.
The group first emerged in December 2023.
It has been widely assessed by private-sector analysts to have ties to the Iranian ecosystem of state-backed operators.
The group reportedly has links to Iran's Ministry of Intelligence and Security (MOIS).
Following the FBI seizure, Handala acknowledged the takedown on its Telegram channel, framing it as censorship.
Their social media account on X was also suspended.
The group maintains two distinct types of online infrastructure.
One domain serves as a propaganda hub cataloging their intrusions.
The other publishes personal data of individuals connected to Israeli defense companies and military operations.
Stryker Attack Details
The Stryker cyberattack represents one of Handala's most disruptive operations to date.
“Law enforcement replaced two Handala websites with seizure banners, signaling an active disruption of the group’s online infrastructure”
It targeted a Fortune 500 medical technology company with more than 56,000 employees across dozens of countries.
According to Handala claims and industry sources, attackers obtained a privileged internal account.
They created a new Global Administrator account to use in their attack.
The breach was particularly destructive in nature.
Attackers moved laterally across Stryker's Windows environment.
They accessed the company's Microsoft Intune management console.
From this privileged position, they issued wipe commands to laptops and mobile devices.
Stryker disclosed it is still restoring computers and internal networks following the breach.
This indicates the severity of the attack.
Attack Technical Significance
The technical nature of the Stryker attack represents a significant evolution in destructive cyber operations.
This is particularly due to the method of abusing mobile device management platforms.

Such approaches are rare because they require highly privileged access.
When successful, the impact can mirror dedicated wiper malware.
Security analysts have drawn parallels to the 2012 Iran-linked Shamoon attack.
That attack erased data on roughly 30,000 Saudi Aramco systems.
The Shamoon attack serves as a benchmark for destructive operations affecting physical industries.
The FBI seizure notice characterized Handala's activities as more than ordinary hacktivism.
The notice explicitly stated U.S. authorities view the operation as involving coordination with a foreign state actor.
This assessment suggests deeper connections between the group and state-sponsored cyber operations.
Broader Cyber Context
The FBI's seizure of Handala's websites comes amid broader patterns of Iran-aligned cyber operations.
“The FBI has seized two websites used by the Handala hacktivist group after the threat actors conducted a destructive cyberattack on medical technology giant Stryker that wiped approximately 80,000 devices”
These operations blend hack-and-leak tactics with data destruction during geopolitical tensions.

Security firms like Mandiant and Microsoft have documented multiple Iran-aligned campaigns following this pattern.
This suggests a deliberate strategy of escalating cyber capabilities during heightened international conflict.
The targeting of Stryker, a major healthcare supplier rather than a hospital, indicates broader objectives.
These objectives extend beyond healthcare infrastructure to the medical technology ecosystem.
The seizure action represents a significant law enforcement response to state-aligned hacktivism.
The FBI took control of domains to disrupt ongoing malicious cyber operations.
They aim to prevent further exploitation by the group.
As investigations continue, details remain limited about the scope of the FBI's access.
It's unclear if they only seized domains or gained access to content and server logs.
More on Technology and Science

Hawaii's Worst Flooding in 20 Years Threatens Dam, Prompts Evacuations as More Rain Looms
11 sources compared

Hawaii Deploys National Guard as Worst Flooding in 20 Years Swamps Oahu
68 sources compared

Heatwave shatters March records as Southwest bakes under extreme temperatures
48 sources compared

Record heat blankets the US Southwest as March logs hottest temperature in Arizona
10 sources compared